The Latest
-
Securing GenAI in the Browser: Policy, Isolation, and Data Controls That Actually Work
-
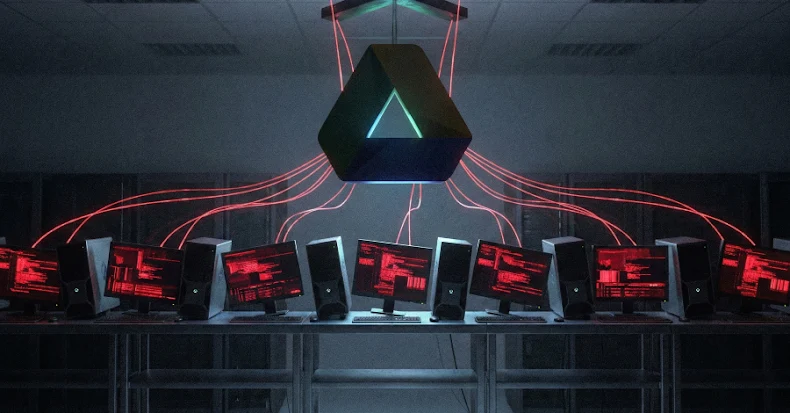
WIRTE Leverages AshenLoader Sideloading to Install the AshTag Espionage Backdoor
-
The Impact of Robotic Process Automation (RPA) on Identity and Access Management
-
NANOREMOTE Malware Uses Google Drive API for Hidden Control on Windows Systems